Mark Certificate Explained: Verified Logo, Trusted Emails
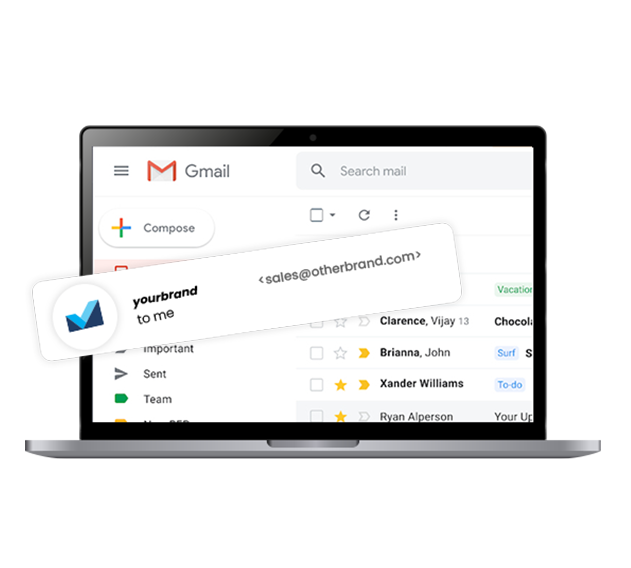
A Mark Certificate acts as a digital verification tool which allows organizations to show their authenticated trademarked logo next to sender name in the recipient’s mailbox.
The Mark Certificate establishes brand credibility by providing verified blue checkmarks as a result of its authentication process.
The complete series of authentication protocols leads to receiving your brand verification checkmark. Your emails automatically gain credibility through the marked logo which appears next to your sender’s name to authenticate your identity before anyone opens the message.
Businesses that adopt Mark certificates enhance their company reputation and differentiate from inbox competition while safeguarding their platforms from malicious activities.
Learn MoreWhy Use a Mark Certificate?
Increase Email Deliverability| Open-Rates.| Security.|
Mark Certificate in 4 Easy Steps
Choose the right Mark Certificate for your Brand
Businesses with or without trademark protection can find a Mark Certificate which boosts trust in inboxes while enhancing visibility and audience engagement.
CMC Includes
- Logo display enabled
- No trademark needed
- DMARC required
- Rapid onboarding process
- Cost-effective solution
- Growing provider support
VMC Includes
- Verified logo display
- Trademark protection needed
- Full DMARC compliance
- Blue checkmark enabled
- High inbox credibility
- Recognized by Gmail & more
Turn your trademark into trust -
before the email is opened.